Table of Contents
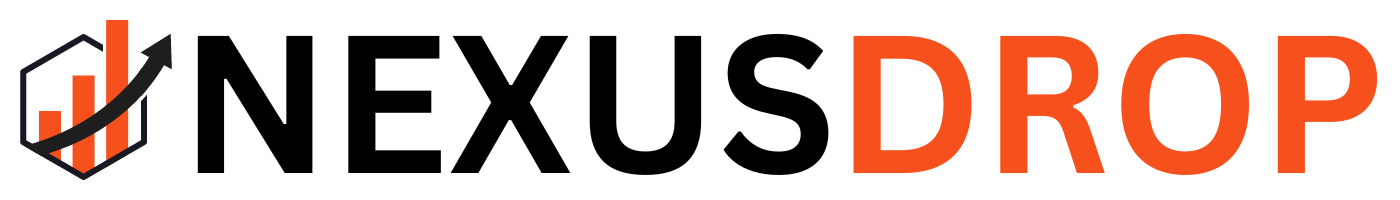
Quick Guide to Strong Password Examples
Creating a secure password is non-negotiable. If you look at strong password examples, you’ll notice they typically aim for at least 14 characters the longer, the better. These secure passcodes should combine uppercase and lowercase letters, digits, and special characters. Alternatively, you can use a series of unrelated words to form a highly secure passphrase.
Password Length
Length is your first line of defense. A password under 12 characters is weak. Aim for 14 or more. Each additional character exponentially increases security. Use a random password generator to create complex strings.
Strong Passwords
- G3n3r@t3!P@ssw0rd
- 7h1s!s@Str0ngP@ss
- R@nd0mW0rds!2026
- Blue!Sky#42&Green
- This solution: orbit-lantern-ocean
Passphrases
This solution can be quite effective. Combine unrelated words. For example, “coffee-table-sunshine” is memorable and secure. This method reduces human risk by avoiding predictable patterns. Such combinations significantly decrease the likelihood of human risk by making it harder for attackers to guess your passwords.
For creating strong passwords, consider using our Strong Password Generator. This tool can help you create long, unique, random passwords that enhance your security posture.
Top Strong Password Examples for Everyday Use
Using a Password Generator
Utilize a password generator to create long, unique, random passwords. These tools can produce complex strings that are hard to crack. Aim for at least 16 characters. Here’s how to maximize effectiveness:
- Choose a reputable password generator.
- Set parameters for length and complexity.
- Incorporate symbols, numbers, and mixed case.
For instance, a generated password like G3n3r@t3!P@ssw0rd or 7h1s!s@Str0ngP@ss demonstrates the right mix of characters. These passwords are not only secure but also difficult for attackers to guess. Weak passwords increase human risk, making it easier for attackers to compromise accounts and sensitive information.
Creating Memorable Passphrases
Passphrases can be both secure and easy to remember. Combine unrelated words to form a memorable sequence. For example, coffee-table-sunshine is effective. This method reduces human risk by avoiding predictable patterns.
- Use at least four unrelated words. This approach not only enhances memorability but also significantly mitigates human risk associated with common password choices.
- Incorporate numbers or symbols for added complexity. Consider using passwords passphrases that are memorable yet complex, enhancing both security and ease of recall. By blending these elements, passwords passphrases become robust defenses against unauthorized access, setting a clear distinction between strong and weak password practices.
- Make it personal but not obvious. Consider using passkeys as a modern alternative to traditional passwords for enhanced security and convenience.
Consider a passphrase like orbit-lantern-ocean. It’s long, unique, and random enough to withstand brute-force attacks. For more insights on crafting secure passwords, check out Sticky Password. Consider using a password manager like sosafe to generate and store complex passwords securely.
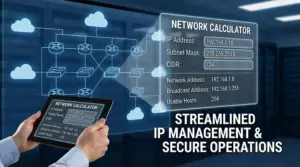
Comparing Strong Passwords: Best Practices vs. Weak Passwords
Identifying Weak Passwords
Weak passwords are an open invitation for hackers. They often include easily guessable elements like birthdays, names, or simple sequences. Here’s what to watch for:
- Common words or phrases.
- Sequential numbers (e.g., 123456).
- Keyboard patterns (e.g., qwerty).
- Personal information (e.g., pet names).
- Short length (under 8 characters).
These passwords are vulnerable to brute-force attacks. Attackers can crack them in seconds using automated tools. Avoid these pitfalls to enhance your security posture.
Characteristics of Strong Passwords
A strong secure password is your first line of defense. It should be long, unique, and complex. Here are key characteristics:
- At least 12-16 characters long.
- A mix of uppercase and lowercase letters.
- Inclusion of numbers and special characters.
- Avoidance of dictionary words or predictable patterns.
- Use of a password generator for randomness.
Consider using a passphrase like orbit-lantern-ocean. It’s memorable and robust against attacks. For added security, leverage a random password generator to create unique combinations. This tool minimizes human risk and enhances your overall security strategy.
Enhancing Security with Multi Factor Authentication
What is Multi-Factor Authentication?
Multi-factor authentication (MFA) adds an extra layer to your security. It requires at least two forms of verification before granting access. This can include something you know (like a password), something you have (like a token), or something you are (like a fingerprint).
Benefits of Multi-Factor Authentication
MFA significantly reduces the risk of unauthorized access. Here’s how:
- Increased Security: Even if a password is compromised, the account remains protected.
- Human Risk Mitigation: Reduces the impact of social engineering attacks.
- Compliance: Many regulations require MFA for sensitive data access.
- Flexibility: Supports various authentication methods, including biometrics and hardware tokens.
- Cost-Effective: Implementing MFA is often cheaper than dealing with breaches.
Implementing MFA can be straightforward. Choose a reliable tool that supports various authentication methods. Ensure it integrates seamlessly with your existing systems. Regularly review and update your authentication methods to stay ahead of threats.
With MFA, you build a security culture that prioritizes data protection. This framework not only safeguards your information but also instills confidence in users. In a landscape where breaches are common, adopting multi-factor authentication is a critical step in enhancing information security.
Frequently Asked Questions
What is an example of a powerful password?
A powerful password example is ‘G7!rT9@qZ3#xL2’. This password combines uppercase letters, lowercase letters, numbers, and special characters, making it complex and difficult to guess. Strong password examples should avoid dictionary words and predictable patterns, ensuring maximum security.
What is a 12 strong password example?
A 12 strong password example is ‘P@ssw0rd!2023#XyZ’. This password includes a mix of uppercase letters, lowercase letters, numbers, and special characters. Using strong password examples like this one enhances security and protects against unauthorized access.
What is a strong 10 character password example?
A strong 10 character password example is ‘Xy!7zQ@2bL’. This password features a combination of uppercase letters, lowercase letters, numbers, and special characters. Utilizing strong password examples like this one is essential for maintaining account security.
Conclusion: Implementing Strong Password Examples for Better Security
Understanding Password Complexity
To combat force attacks, use long, unique, random passwords. Aim for at least 12 characters. Incorporate uppercase, lowercase, numbers, and symbols. This framework significantly reduces vulnerability.
Utilizing Passphrases
Passphrases are effective. They are easier to remember and can be highly secure. For example, “blue-sky!7dolphin” combines words with symbols and numbers. This method enhances memorability while maintaining strength.
MultiFactor Authentication
Implement multifactor authentication (MFA) for added security. This requires a second verification step, such as a code sent to your phone. MFA drastically lowers the risk of unauthorized access.
Password Managers
Use password managers like NordPass to generate and store random passwords. They can create complex passwords that you don’t have to remember. This tool mitigates human risk by eliminating the need for memory-based passwords.
Best Practices for Account Security
- Regularly update passwords.
- Avoid reusing passwords across accounts.
- Use a random password generator for new accounts.
- Consider using a password manager for convenience.
Implementing these strategies will bolster your security posture. Strong passwords, passphrases, and multi-factor authentication are essential components of a robust security framework.