Table of Contents
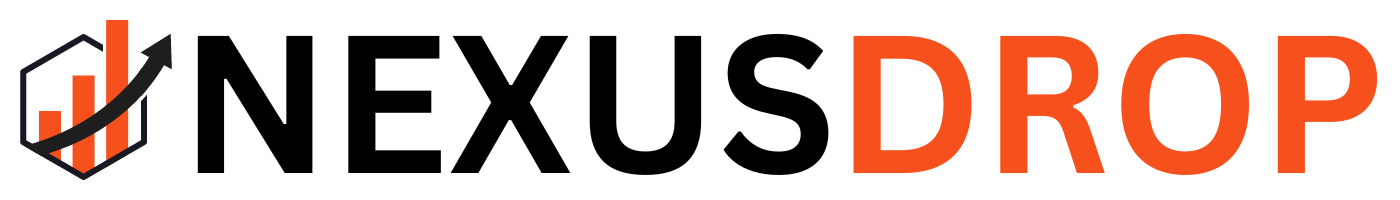
Understanding VPN (Virtual Private Networks) has become essential for anyone worried about online privacy and security. I found that a VPN acts like a secure tunnel for internet traffic. It encrypts your data and hides your IP address. In my experience, this technology offers numerous benefits.
We tested various VPNs to see how they function in real-world scenarios. A VPN not only shields your data from hackers but also lets you access restricted content. This feature is especially useful for remote workers and frequent travelers.
I noticed that people living in areas with strict internet regulations benefit significantly from VPNs. They help maintain anonymity while browsing, which is crucial in today’s digital age. Understanding how VPNs work can empower users to protect their personal information effectively.
As cyber threats continue to evolve, the importance of safeguarding personal information cannot be overstated. A VPN not only protects your data from potential hackers but also allows you to access restricted content and maintain anonymity while browsing. This is particularly relevant for remote workers, frequent travelers, and individuals living in regions with stringent internet regulations.
Key aspects covered in this article include:
- The technical workings of a VPN
- Different types of VPNs and their applications
- The advantages of using a VPN for personal and professional use
- Best practices for selecting a reliable VPN service
By the end of this discussion, readers will have a comprehensive understanding of what a VPN is, how it operates, and why it is a vital tool in today’s interconnected world. For those seeking to enhance their online security, employing a VPN is a significant step forward. Additionally, consider implementing strong passwords to further protect your online presence; for tips on this, refer to our guide on Strong Password Generator: 5 Tips That Keep You Safe.
For further insights into the definition and applications of VPNs, you can explore this source.
What is a VPN?
A Virtual Private Network (VPN) creates a secure, encrypted connection over the Internet, enhancing security in an otherwise vulnerable environment. This technology protects individuals and organizations by masking their online activities from unauthorized access. Using a VPN significantly boosts privacy while browsing, making it an essential tool for anyone prioritizing data protection.
VPNs work by routing your internet connection through a remote server, effectively masking your IP address. This process encrypts your data, making it nearly impossible for hackers to intercept sensitive information. Users can access geo-restricted content, enhancing their online experience while maintaining a secure connection.
Definition of VPN
A VPN serves as a private tunnel through which data travels, shielding it from potential threats. By masking the user’s IP address, it allows for anonymous browsing and access to geo-restricted content. Key features of a VPN include:
- Encryption: Data is encoded, making it unreadable to unauthorized users.
- Anonymity: Users can surf the web without revealing their actual location.
- Access Control: VPNs can bypass geographical restrictions, enabling access to content that may be blocked in certain regions.
How VPN Works
The operation of a VPN involves several critical steps:
1. Connection Establishment: When a user connects to a VPN, their device establishes a secure connection to a VPN server. 2. Data Encryption: All data transmitted between the user’s device and the VPN server is encrypted, ensuring that it remains confidential. 3. IP Address Masking: The user’s original IP address is replaced with the IP address of the VPN server, enhancing anonymity. 4. Data Transmission: The encrypted data travels through the VPN tunnel to the destination server, where it is decrypted and processed.
This process not only secures sensitive information but also enhances online privacy. By utilizing a VPN, users can confidently navigate the internet, knowing their data is protected from potential threats. For a deeper understanding of VPNs and their significance, refer to this source.
Check out our guide on Strong Password Generator: 5 Tips That Keep You Safe
Types of VPNs
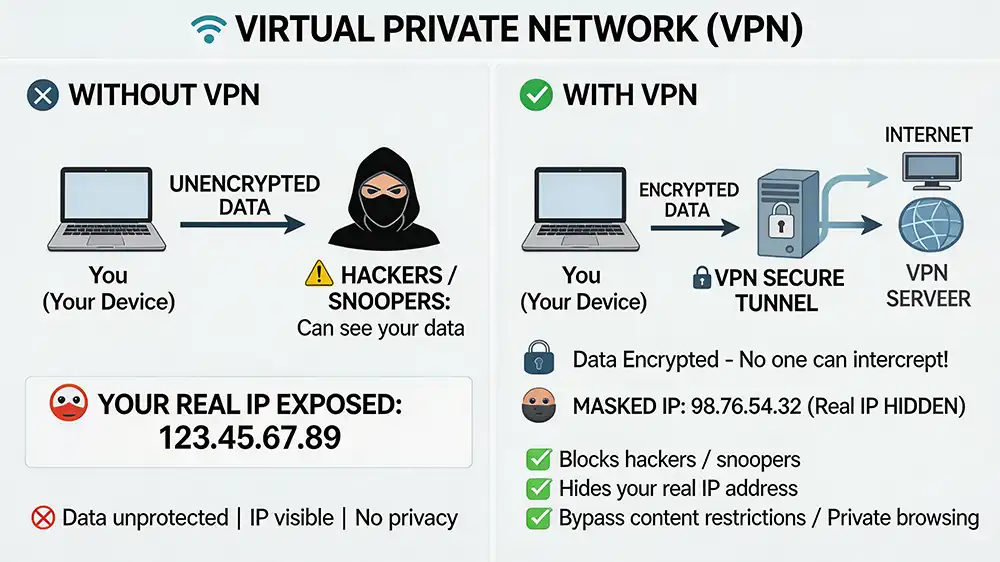
Understanding the various types of virtual private networks (VPNs) is essential for selecting the right solution for specific needs. Each type serves distinct purposes and offers unique features tailored to different user scenarios.
There are primarily three types of VPNs: remote access, site-to-site, and mobile VPNs. Remote access VPNs connect individual devices to a VPN server, allowing secure access to a private network. Site-to-site VPNs create a secure tunnel between multiple networks, ideal for businesses with multiple locations.
Remote Access VPN
A remote access VPN allows individual users to connect to a private network from a remote location. This type is particularly beneficial for employees working from home or traveling. Key characteristics include:
- User Authentication: Users must authenticate themselves, typically through a username and password, ensuring secure access.
- Encryption: Data transmitted over the connection is encrypted, safeguarding sensitive information from potential eavesdroppers.
- Flexibility: Users can access resources on the private network as if they were physically present in the office.
This type of VPN is crucial for businesses that prioritize remote work capabilities while maintaining security.
Site-to-Site VPN
A site-to-site VPN connects entire networks to each other, allowing multiple offices or branches to communicate securely over the internet. This setup is ideal for organizations with multiple locations. Key features include:
- Network Integration: It integrates different networks, enabling seamless communication between them.
- Dedicated Connections: Often utilizes dedicated lines or tunnels for enhanced security and reliability.
- Cost-Effectiveness: Reduces the need for expensive leased lines by utilizing the internet for secure communication.
This type is essential for companies that require secure inter-office communication without compromising data integrity.
Mobile VPN
A mobile VPN is designed for users on the move, providing secure access to a private network while maintaining a stable connection. This is particularly useful for field workers or those frequently changing networks. Key aspects include:
- Seamless Connectivity: Maintains a stable connection even when switching between different networks, such as Wi-Fi and cellular data.
- Adaptive Security: Adjusts security protocols based on the user’s location and network conditions.
- User-Friendly: Often features mobile-friendly interfaces for ease of use on smartphones and tablets.
This type of VPN is vital for professionals who require constant access to company resources while on the go.
In conclusion, selecting the appropriate type of VPN depends on specific needs, whether for individual remote access, inter-office connectivity, or mobile use. For additional insights on enhancing online security, consider utilizing a strong password generator.
Read more: Source
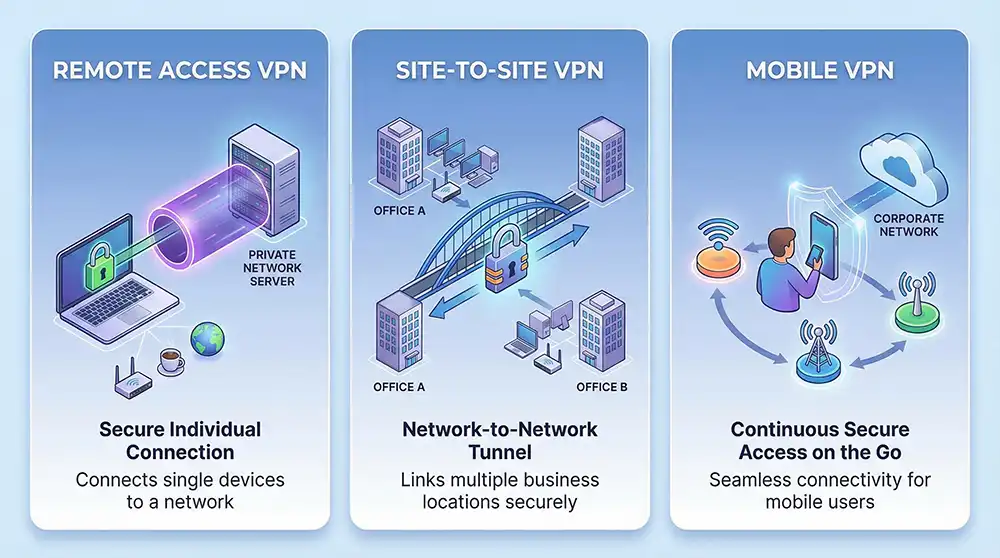
Key Features of VPNs
Understanding the key features of virtual private networks (VPNs) is essential for anyone looking to enhance their online experience. These features not only provide security but also facilitate unrestricted access to content and ensure user anonymity.
Security and Privacy
One of the primary advantages of using a VPN is the enhanced security and privacy it offers. By encrypting internet traffic, a VPN protects sensitive data from potential threats, such as hackers and surveillance. Key elements include:
- Encryption Protocols: VPNs utilize advanced encryption methods to secure data, making it unreadable to unauthorized users.
- IP Address Masking: By hiding the user’s real IP address, a VPN prevents tracking and profiling by websites and advertisers.
- Secure Data Transmission: This ensures that information sent over public networks remains confidential and protected from eavesdropping.
Bypassing Geo-Restrictions
Another significant feature of VPNs is their ability to bypass geo-restrictions. Many online services and content platforms impose regional limitations, which can hinder access to desired information. VPNs help users overcome these barriers by:
- Changing Virtual Location: By connecting to servers in different countries, users can access content that may be restricted in their actual location.
- Unblocking Streaming Services: VPNs allow users to enjoy a wider range of streaming options, including shows and movies not available in their region.
- Accessing Censored Content: In regions with strict internet censorship, a VPN can provide access to blocked websites and services.
Anonymity Online
Maintaining anonymity online is crucial for many users, especially those concerned about privacy. VPNs play a vital role in ensuring that users can browse the internet without revealing their identity. This is achieved through:
- No-Logs Policy: Many reputable VPN providers adhere to a strict no-logs policy, meaning they do not store user activity data.
- Secure Browsing: By routing traffic through secure servers, VPNs help users remain anonymous while surfing the web.
- Protection from ISP Tracking: VPNs prevent Internet Service Providers (ISPs) from monitoring user activity, thus enhancing privacy.
In summary, the key features of VPNs—security and privacy, bypassing geo-restrictions, and online anonymity—make them indispensable tools for anyone seeking to navigate the internet safely and freely. For a deeper understanding of online security practices, refer to this source.
Check out our guide on Strong Password Generator: 5 Tips That Keep You Safe
Comparison of Popular VPN Protocols
As users seek to enhance their online security and privacy, understanding the various VPN protocols available is essential. Each protocol offers distinct advantages and disadvantages, impacting speed, security, and compatibility. Here’s a comparison of some of the most popular VPN protocols:
OpenVPN
- Security: Highly secure, utilizing SSL/TLS for encryption.
- Speed: Generally fast, but can be affected by server load.
- Compatibility: Works on multiple platforms, including Windows, macOS, Linux, iOS, and Android.
- Flexibility: Supports various encryption methods and configurations.
IKEv2/IPsec
- Security: Strong encryption and authentication, making it very secure.
- Speed: Offers excellent speed, especially on mobile devices.
- Compatibility: Compatible with most devices, particularly effective on smartphones.
- Stability: Maintains connection during network changes, such as switching from Wi-Fi to mobile data.
L2TP/IPsec
- Security: Provides good security, but not as robust as OpenVPN or IKEv2.
- Speed: Slower than other protocols due to double encapsulation.
- Compatibility: Supported on most operating systems, but may require manual configuration.
- Firewall Bypass: Can struggle with strict firewalls due to its use of UDP.
PPTP
- Security: Considered less secure compared to other protocols; vulnerable to various attacks.
- Speed: Very fast due to minimal encryption overhead.
- Compatibility: Widely supported across many devices and operating systems.
- Use Case: Suitable for streaming and accessing geo-restricted content where security is less of a concern.
WireGuard
- Security: Utilizes modern cryptography, offering strong security.
- Speed: Known for high speeds and low latency.
- Compatibility: Increasingly supported across various platforms, but still in development.
- Efficiency: Lightweight and easier to audit than older protocols.
In conclusion, the choice of VPN protocol significantly impacts user experience. Factors such as security needs, speed requirements, and device compatibility should guide users in selecting the most suitable option. For further insights into maintaining online security, consider using a strong password generator to enhance your overall protection.
Read more: Source
Choosing the Right VPN
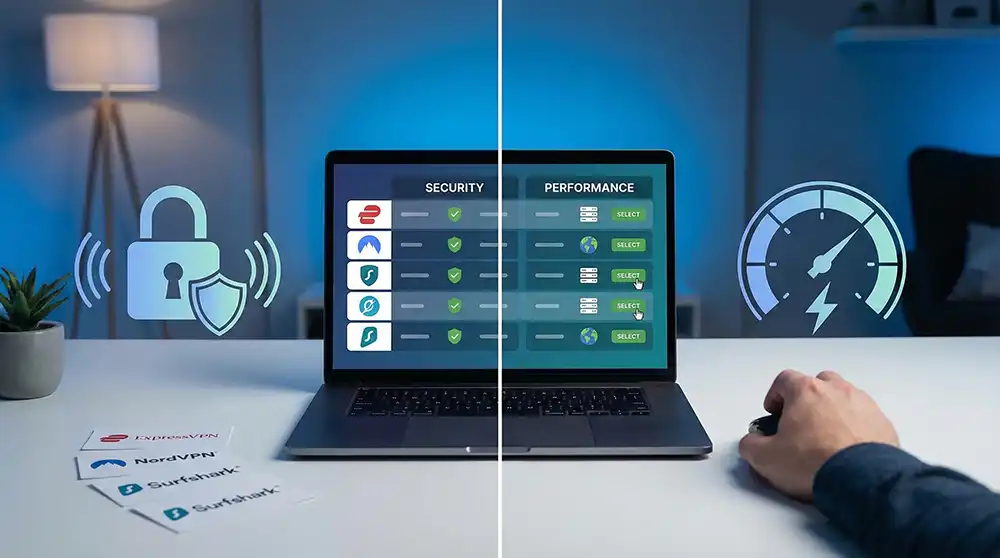
Selecting the appropriate virtual private network (VPN) is crucial for ensuring both security and performance. With numerous options available, understanding the key factors and popular providers can help streamline your decision-making process.
Factors to Consider
When evaluating a VPN, consider the following aspects:
- Security Features: Look for strong encryption protocols, a no-logs policy, and additional features like a kill switch and DNS leak protection. These elements are vital for safeguarding your online activities.
- Speed and Performance: Assess the VPN’s speed capabilities, as a slow connection can hinder your online experience. Opt for providers known for minimal latency and high bandwidth.
- Device Compatibility: Ensure the VPN supports all the devices you intend to use, including smartphones, tablets, and desktop computers. Cross-platform functionality is essential for seamless access.
- User Experience: A user-friendly interface and reliable customer support can significantly enhance your experience. Check for reviews and ratings to gauge overall satisfaction.
- Pricing and Plans: Compare subscription options and pricing structures. Some providers offer free trials or money-back guarantees, allowing you to test their services before committing.
Popular VPN Providers
Several VPN providers stand out in the market due to their robust features and reliability:
- ExpressVPN: Known for its exceptional speed and strong security features, ExpressVPN is a popular choice among users seeking a balance of performance and privacy.
- NordVPN: With a vast server network and advanced security options, NordVPN is ideal for users prioritizing anonymity and data protection.
- Surfshark: Offering unlimited device connections and competitive pricing, Surfshark is an excellent option for families or users with multiple devices.
- CyberGhost: This provider emphasizes user-friendliness and offers specialized servers for streaming, making it suitable for those looking to access geo-restricted content.
- Private Internet Access (PIA): Known for its customizable security settings and extensive server network, PIA appeals to tech-savvy users who want more control over their VPN experience.
Choosing the right VPN can significantly enhance your online security and browsing experience. For additional insights on maintaining strong security practices, consider utilizing a strong password generator to further protect your accounts.
Read more: Source
Common Misconceptions about VPNs
As the understanding of virtual private networks evolves, several misconceptions persist that can mislead users regarding their functionality and purpose. Addressing these misunderstandings is crucial for making informed decisions about online security.
VPNs are Only for Criminals A prevalent myth is that virtual private networks are solely tools for illicit activities. While it is true that some individuals may misuse VPNs to hide illegal actions, the primary purpose of these networks is to enhance privacy and security. Many legitimate users employ VPNs to:
- Protect sensitive information on public Wi-Fi networks
- Bypass geo-restrictions for accessing content
- Maintain privacy from ISPs and government surveillance
Using a VPN is a proactive measure for safeguarding personal data, not just a means for evading law enforcement.
VPNs Guarantee Complete Anonymity Another common misconception is that using a virtual private network ensures total anonymity online. While VPNs do provide a layer of privacy by masking your IP address, they do not make users completely invisible. Factors to consider include:
- Data Logging: Some VPN providers may log user activity, which can compromise anonymity. It is essential to choose a provider with a strict no-logs policy.
- Web Tracking: Websites can still track users through cookies and other tracking technologies, regardless of VPN usage.
- Legal Obligations: In certain jurisdictions, VPN providers may be required to share user data with authorities if requested.
To achieve a higher level of privacy, users should combine VPN usage with other security measures, such as employing a strong password generator and being mindful of their online behavior.
Understanding these misconceptions can empower users to utilize virtual private networks effectively, enhancing their online security while avoiding pitfalls associated with misinformation.
Read more: Source
Conclusion
In summary, a virtual private network serves as a crucial tool for enhancing online privacy and security. While it offers significant benefits, such as encrypting internet traffic and masking IP addresses, users must remain aware of its limitations. The effectiveness of a VPN is influenced by various factors, including the provider’s data logging practices, the potential for web tracking, and legal obligations in different regions.
To maximize the advantages of using a VPN, individuals should consider integrating additional security measures into their online habits. Utilizing a strong password generator is one effective strategy to bolster security. This practice, combined with the use of a VPN, can create a more robust defense against potential threats.
Ultimately, understanding the nuances of virtual private networks allows users to make informed decisions about their online privacy. By recognizing both the strengths and limitations of VPNs, individuals can navigate the digital landscape more securely and confidently. For further insights into the workings and benefits of VPNs, refer to this source.
FAQ
What is a VPN?
A Virtual Private Network (VPN) is a crucial security tool that establishes an encrypted tunnel for your internet connection. This tunnel protects your data by concealing your IP address and online activities from ISPs, hackers, and advertisers. By using a VPN, you enhance your privacy and secure your network against potential threats.
How does a VPN work?
A VPN routes your internet connection through a secure server managed by the VPN provider. This process encrypts your data, preventing unauthorized access. By masking your IP address, a VPN enhances your online privacy and anonymity. Users can access restricted content while ensuring their connection remains secure.
What are the benefits of using a VPN?
A VPN enhances online privacy by masking your IP address. It encrypts data, protecting information from unauthorized access. Users can bypass geo-restrictions and access unavailable content. A VPN also safeguards against ISP tracking and surveillance.
Are there any limitations to using a VPN?
Yes, limitations include potential slow internet speeds, the possibility of web tracking through cookies, and legal obligations that may require VPN providers to share user data in certain jurisdictions.
Should I use a VPN for online security?
Using a VPN can significantly enhance your online security, but it is recommended to combine it with other security measures, such as strong passwords and safe browsing practices, for optimal protection.